Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
PayPal Flaw Exposed Email Addresses, Social Security Numbers for 6 Months
PayPal disclosed a software error in its Working Capital platform that exposed sensitive customer data, including Social Security numbers, for months in 2025. The post PayPal Flaw Exposed Email Addresses, Social Security Numbers for 6 Months appeared first on...
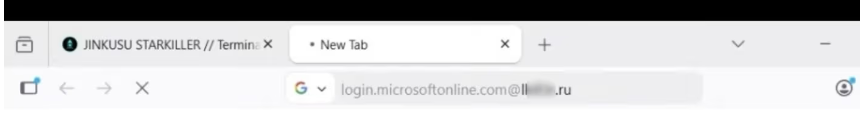
‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA
Most phishing websites are little more than static copies of login pages for popular online destinations, and they are often quickly taken down by anti-abuse activists and security firms. But a stealthy new phishing-as-a-service offering lets customers sidestep both...
Google Blocked 1.75M Harmful Apps From Play Store in 2025
Google used AI-driven review systems to block 1.75 million policy-violating apps and ban 80,000 developer accounts in 2025, expanding Play Store and Android security enforcement. The post Google Blocked 1.75M Harmful Apps From Play Store in 2025 appeared first on...
Microsoft: Critical Security Issue Found in Windows Notepad
Microsoft patches CVE-2026-20841, a high-severity Windows Notepad flaw that could allow code execution via malicious Markdown files. The post Microsoft: Critical Security Issue Found in Windows Notepad appeared first on TechRepublic.
BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
Threat actors have been observed exploiting a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products to conduct a wide range of malicious actions, including deploying VShell and The...
Scammers Use Fake Gemini AI Chatbot for Crypto Scam
Scammers used a fake Gemini AI chatbot to promote a bogus Google Coin presale, signaling a rise in AI-driven crypto impersonation fraud. The post Scammers Use Fake Gemini AI Chatbot for Crypto Scam appeared first on TechRepublic.
Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
In yet another software supply chain attack, the open-source, artificial intelligence (AI)-powered coding assistant Cline CLI was updated to stealthily install OpenClaw, a self-hosted autonomous AI agent that has become exceedingly popular in the past few months. "On...
ClickFix Campaign Abuses Compromised Sites to Deploy MIMICRAT Malware
Cybersecurity researchers have disclosed details of a new ClickFix campaign that abuses compromised legitimate sites to deliver a previously undocumented remote access trojan (RAT) called MIMICRAT (aka AstarionRAT). "The campaign demonstrates a high level of...
Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
With one in three cyber-attacks now involving compromised employee accounts, insurers and regulators are placing far greater emphasis on identity posture when assessing cyber risk. For many organizations, however, these assessments remain largely opaque. Elements...
Ukrainian National Sentenced to 5 Years in North Korea IT Worker Fraud Case
A 29-year-old Ukrainian national has been sentenced to five years in prison in the U.S. for his role in facilitating North Korea's fraudulent information technology (IT) worker scheme. In November 2025, Oleksandr "Alexander" Didenko pleaded guilty to wire fraud...
