Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
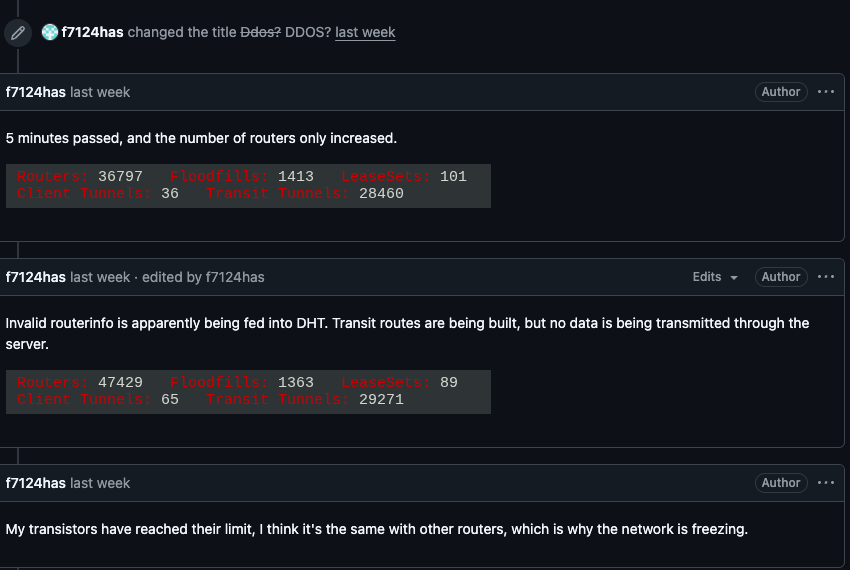
Kimwolf Botnet Swamps Anonymity Network I2P
For the past week, the massive “Internet of Things” (IoT) botnet known as Kimwolf has been disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users started...
Google Expands ‘Results About You’ to Shield IDs, Fight Deepfake Abuse
Google expands its “Results about you” tool to remove sensitive IDs and explicit images from Search, strengthening privacy protections amid rising identity theft. The post Google Expands ‘Results About You’ to Shield IDs, Fight Deepfake Abuse appeared first on...
Waikiki Drone Plan Sparks Privacy Pushback
Hawaii plans to use "first responder" drones in Waikiki to reach crime scenes and emergencies faster, and privacy advocates are sounding the alarm. The post Waikiki Drone Plan Sparks Privacy Pushback appeared first on TechRepublic.
APT36 and SideCopy Launch Cross-Platform RAT Campaigns Against Indian Entities
Indian defense sector and government-aligned organizations have been targeted by multiple campaigns that are designed to compromise Windows and Linux environments with remote access trojans capable of stealing sensitive data and ensuring continued access to infected...
Over 60 Software Vendors Issue Security Fixes Across OS, Cloud, and Network Platforms
It's Patch Tuesday, which means a number of software vendors have released patches for various security vulnerabilities impacting their products and services. Microsoft issued fixes for 59 flaws, including six actively exploited zero-days in various Windows components...
Exposed Training Open the Door for Crypto-Mining in Fortune 500 Cloud Environments
Intentionally vulnerable training applications are widely used for security education, internal testing, and product demonstrations. Tools such as OWASP Juice Shop, DVWA, Hackazon, and bWAPP are designed to be insecure by default, making them useful for learning how...
Microsoft Patches 59 Vulnerabilities Including Six Actively Exploited Zero-Days
Microsoft on Tuesday released security updates to address a set of 59 flaws across its software, including six vulnerabilities that it said have been exploited in the wild. Of the 59 flaws, five are rated Critical, 52 are rated Important, and two are rated Moderate in...
SSHStalker Botnet Uses IRC C2 to Control Linux Systems via Legacy Kernel Exploits
Cybersecurity researchers have disclosed details of a new botnet operation called SSHStalker that relies on the Internet Relay Chat (IRC) communication protocol for command-and-control (C2) purposes. "The toolset blends stealth helpers with legacy-era Linux...
North Korea-Linked UNC1069 Uses AI Lures to Attack Cryptocurrency Organizations
The North Korea-linked threat actor known as UNC1069 has been observed targeting the cryptocurrency sector to steal sensitive data from Windows and macOS systems with the ultimate goal of facilitating financial theft. "The intrusion relied on a social engineering...

Patch Tuesday, February 2026 Edition
Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild. Zero-day #1 this month is...
