Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
Vietnam-Based Hackers Steal Financial Data Across Asia with Malware
A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest valuable data since at least May 2023. Cisco Talos is tracking the cluster under the name CoralRaider,...
New Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. "The phishing emails use a unique vehicle incident lure and, in later stages of the infection chain, spoof the Federal...
New Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. "The phishing emails use a unique vehicle incident lure and, in later stages of the infection chain, spoof the Federal...
AI Deepfakes Rising as Risk for APAC Organisations
A cyber security expert from Tenable has called on large tech platforms to do more to identify AI deepfakes for users, while APAC organisations may need to include deepfakes in risk assessments.
Asia-Pacific Ransomware Threats Depend on Country and Sector, Says Rapid7
Cyber security operatives have been warned to look at the specific ransomware threats facing their country and industry, while closing down common pathways being used by skilled access brokers.
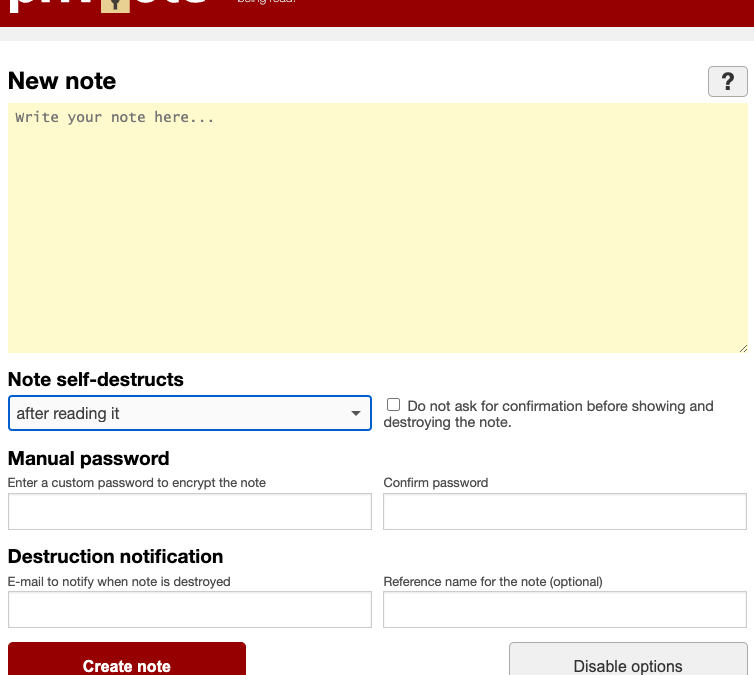
Fake Lawsuit Threat Exposes Privnote Phishing Sites
A cybercrook who has been setting up websites that mimic the self-destructing message service privnote.com accidentally exposed the breadth of their operations recently when they threatened to sue a software company. The disclosure revealed a profitable network of...
Get a Lifetime of VPN Protection for Just $16
During a special sale event, you can get an extra 20% off our already discounted price on RealVPN, bringing it down to just $16 for life. Use code SECURE20 at checkout.
5 Best Password Managers for Android in 2024
Explore the best password managers for Android devices that offer secure storage and easy access to your passwords. Find out which one suits your needs best.
Considerations for Operational Technology Cybersecurity
Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise's physical devices, processes, and events. Unlike traditional Information Technology (IT) systems, OT systems directly impact the physical world. This...
New HTTP/2 Vulnerability Exposes Web Servers to DoS Attacks
New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique has been codenamed HTTP/2 CONTINUATION Flood by security researcher Bartek Nowotarski, who reported the issue to the...
