Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
New Phishing Kit Leverages SMS, Voice Calls to Target Cryptocurrency Users
A novel phishing kit has been observed impersonating the login pages of well-known cryptocurrency services as part of an attack cluster designed to primarily target mobile devices. “This kit enables attackers to build carbon copies of single sign-on (SSO) pages, then...
4 Instructive Postmortems on Data Downtime and Loss
More than a decade ago, the concept of the ‘blameless’ postmortem changed how tech companies recognize failures at scale. John Allspaw, who coined the term during his tenure at Etsy, argued postmortems were all about controlling our natural reaction to an incident,...
New BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive domain mimicking VMware. "This latest version of Bifrost aims to bypass security measures and compromise targeted systems,"...
Five Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in Ivanti Connect Secure and Ivanti Policy Secure gateways, noting that the Integrity Checker Tool (ICT) can be deceived...
GitHub Rolls Out Default Secret Scanning Push Protection for Public Repositories
GitHub on Thursday announced that it’s enabling secret scanning push protection by default for all pushes to public repositories. “This means that when a supported secret is detected in any push to a public repository, you will have the option to remove the secret...
Dashlane Free vs. Premium: Which Plan Is Best For You?
Compare the features and benefits of Dashlane's free and premium versions to determine which option is best for your password management needs.
NordPass Free vs. Premium: Is It Worth the Upgrade?
NordPass offers both Free and Premium versions. Learn about the differences and features of each version to determine which one is right for you.
Proton VPN Free vs. Premium: Which Plan Is Best For You?
Compare the features, benefits and limitations of Proton VPN's free and paid versions to determine which option is best for your privacy and security needs.
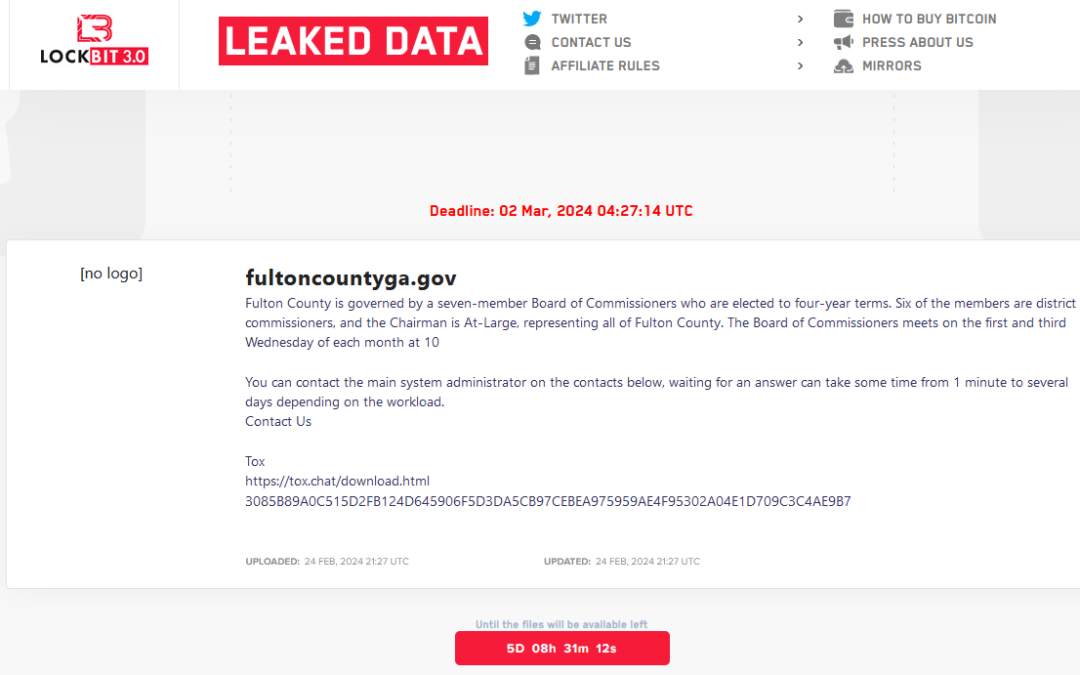
Fulton County, Security Experts Call LockBit’s Bluff
The ransomware group LockBit told officials with Fulton County, Ga. they could expect to see their internal documents published online this morning unless the county paid a ransom demand. LockBit removed Fulton County’s listing from its victim shaming website this...
RoboForm Free vs. Paid: Which Plan Is Best For You?
Explore the differences between RoboForm's free and paid versions, and decide which one is the right fit for your organization.
