Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
Best Secure Access Service Edge Platforms in 2024
Here are the top Secure Access Service Edge platforms that provide security and network functionality. Find the best SASE solution for your business needs.
Speedify VPN Free vs. Premium: Which Plan Is Right For You?
Explore the differences between Speedify VPN Free and Premium versions, including features, benefits and which one is the best fit for your needs.
hide.me VPN Free vs. Premium: Which Plan Is Right For You?
Compare the differences between hide.me VPN's free and premium versions. Find out about the features, pros and cons of each option.
TunnelBear VPN Free vs. Paid: Which Plan Is Right for You?
TunnelBear VPN offers both free and paid versions, each with its own set of pros and cons. Learn about the differences and decide which one is right for you.
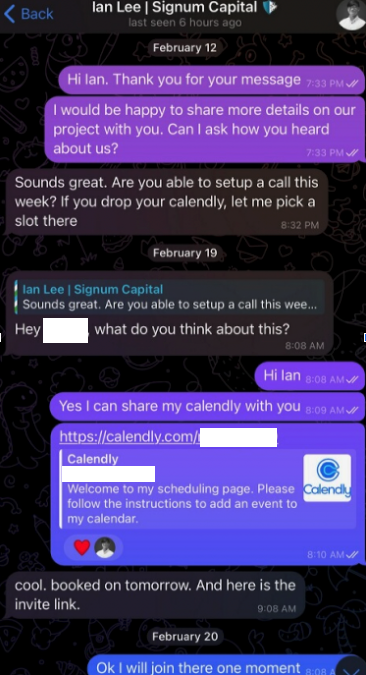
Calendar Meeting Links Used to Spread Mac Malware
Malicious hackers are targeting people in the cryptocurrency space in attacks that start with a link added to the target’s calendar at Calendly, a popular application for scheduling appointments and meetings. The attackers impersonate established cryptocurrency...
Hotspot Shield VPN Free vs. Premium: Which Is Right For You?
Hotspot Shield VPN offers both a free and premium version. Learn about the differences between the two options and decide which one is right for you.
10 Must-Read Books on Cybersecurity
In a world fraught with cyberattacks and privacy violations in both business and individual spaces, cybersecurity remains a veritable tool for curtailing these attacks and improving privacy practices. But how can we put cybersecurity to good use without having a...
Iran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation, and defense industries in the Middle East, including Israel and the U.A.E. Other targets of the cyber espionage activity...
FBI Warns U.S. Healthcare Sector of Targeted BlackCat Ransomware Attacks
The U.S. government is warning about the resurgence of BlackCat (aka ALPHV) ransomware attacks targeting the healthcare sector as recently as this month. "Since mid-December 2023, of the nearly 70 leaked victims, the healthcare sector has been the most commonly...
Building Your Privacy-Compliant Customer Data Platform (CDP) with First-Party Data
In today's digital era, data privacy isn't just a concern; it's a consumer demand. Businesses are grappling with the dual challenge of leveraging customer data for personalized experiences while navigating a maze of privacy regulations. The answer? A privacy-compliant...
