Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
Learn How to Protect Your Business With Ultimate Security for $80
Protect your company by learning maximum security practices in this bundle, while it's available at the best-on-web price of only $79.99.
Rust-based Realst Infostealer Targeting Apple macOS Users’ Cryptocurrency Wallets
A new malware family called Realst has become the latest to target Apple macOS systems, with a third of the samples already designed to infect macOS 14 Sonoma, the upcoming major release of the operating system. Written in the Rust programming language, the malware is...
Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking
A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors to execute arbitrary code and seize full control of vulnerable devices. Cataloged as CVE-2023-30799 (CVSS score: 9.1), the shortcoming is expected to put...
Who and What is Behind the Malware Proxy Service SocksEscort?
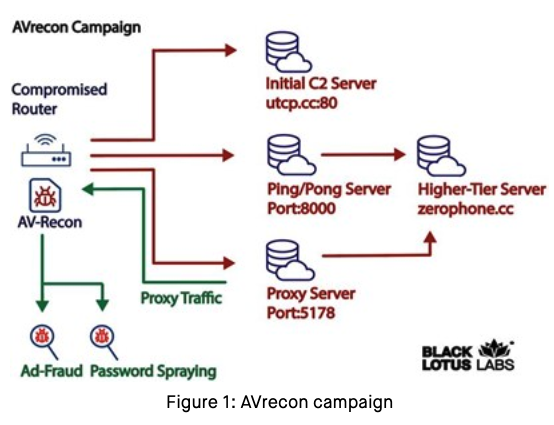
Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed AVrecon that enslaves Internet routers into botnet that bilks online advertisers and performs password-spraying attacks. Now new findings reveal that AVrecon is the malware engine...
Get 8 Months of Live Cyber Security Training for Under $500
If you're new to cyber security or trying to improve your knowledge, Cyber Security Specialist Workshop Live Sessions provides 32 weeks of essential training for under $500.
Checklist: Securing Digital Information
Digital information is generally the lifeblood of any given organization, containing essential company data needed to run the business. Paperless offices have become the norm across industries and remote work depends on the ability to share electronic information for...
North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder
North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational security (OPSEC) blunder that exposed their actual IP address. Google-owned threat intelligence firm Mandiant...
Casbaneiro Banking Malware Goes Under the Radar with UAC Bypass Technique
The financially motivated threat actors behind the Casbaneiro banking malware family have been observed making use of a User Account Control (UAC) bypass technique to gain full administrative privileges on a machine, a sign that the threat actor is evolving their...
macOS Under Attack: Examining the Growing Threat and User Perspectives
As the number of people using macOS keeps going up, so does the desire of hackers to take advantage of flaws in Apple's operating system. What Are the Rising Threats to macOS? There is a common misconception among macOS fans that Apple devices are immune to hacking...
How to Create a Custom Security & Threat Dashboard in Power BI
Want a custom security dashboard to bring together data from multiple places? Microsoft Power BI can do that and help you spot what's changing.
