Blog
Our latest news.
Stay up-to-date with news and blog posts from ASMGi on how to bridge the gap to apply technology to solve business problems.
ASMGi Posts

IT Chaos Solved: Intune + Autopilot in Action

Fail SOC 2 Once – Pay Forever

Essential AI Strategies to Strengthen Third Party Risk Management

Cyber Insurance: Making the Most of Your Policy

Preventing Breaches: The Power of Security Awareness Training

Webinar: Resiliency in the Face of Ransomware

Zero Trust: A Paradigm Shift in Cybersecurity

Unveiling Deception: How to Spot Scams Before They Spot You

Ransomware: Strategies for Safeguarding Your Digital Assets

Unraveling the Power of AI in Cybersecurity: Safeguarding the Digital Realm

Fortifying Cybersecurity Defenses

Optimizing Healthcare Cybersecurity Cost and Staffing: Balancing Resources and Risk in Healthcare

Leading Cybersecurity Companies GS Lab | GAVS and ASMGi Announce Strategic Partnership to Enhance Global Cyber Defense

Understanding the Importance of Third-Party Risk Management in Healthcare

Embracing Smart Manufacturing: Unveiling IoT Trends, Challenges, and Cybersecurity in the Era of Industry 4.0
Cybersecurity Update – Terin D. Williams – DHS – CISA

Real Life Cyber Attacks - Dec 1 Event

The age of IoT and AI is quickly advancing, demanding more compute power and lower latency at the edge to ensure quick response and great performance.

xIoT Device Risk: Turning the Industry Inside-Out

Cyber Insurance: Digital Risk Mitigation Plan From Financial Loss

AI In Healthcare
Cybersecurity News from Around the Web
The State of Security 2023
Cyberattacks continue to grow in quantity and sophistication at the same time that organizations’ systems become increasingly complex. Security teams, as always, feel the stress. But a surprising outcome of our 2023 State of Security research is that the number of...
Information Security Policy
This policy from TechRepublic Premium provides guidelines to safeguard company information, reduce business and legal risks and protect company investments and reputation. It covers data. Its adjunct policy, the Network security policy, covers the systems and devices...
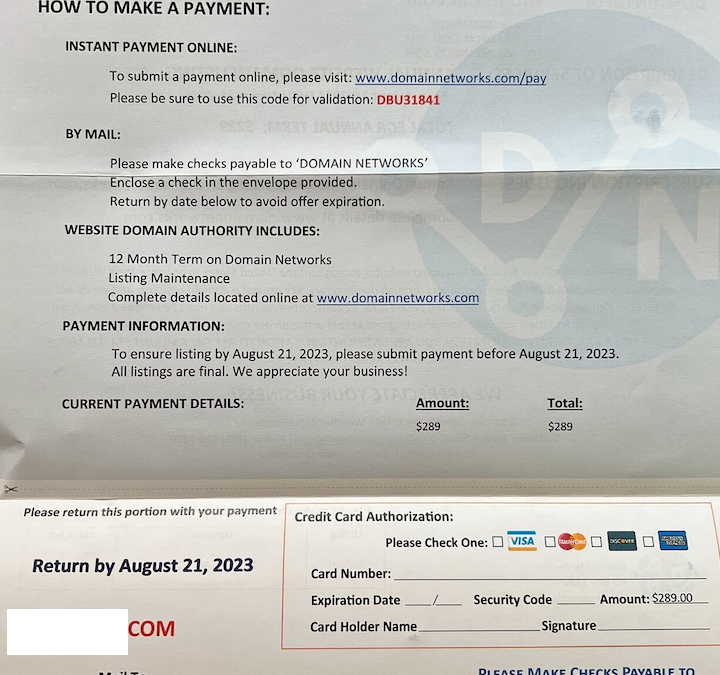
Who’s Behind the DomainNetworks Snail Mail Scam?
If you’ve ever owned a domain name, the chances are good that at some point you’ve received a snail mail letter which appears to be a bill for a domain or website-related services. In reality, these misleading missives try to trick people into paying for useless...
How to add the Docker Scout feature to the Docker CLI
In this TechRepublic How to Make Tech Work tutorial, Jack Wallen shows you how to add the Docker Scout feature to the Docker CLI. The post How to add the Docker Scout feature to the Docker CLI appeared first on TechRepublic.
Chinese Hackers Use HTML Smuggling to Infiltrate European Ministries with PlugX
A Chinese nation-state group has been observed targeting Foreign Affairs ministries and embassies in Europe using HTML smuggling techniques to deliver the PlugX remote access trojan on compromised systems. Cybersecurity firm Check Point said the activity,...
Improve Your Security WordPress Spam Protection With CleanTalk Anti-Spam
Every website owner or webmaster grapples with the issue of spam on their website forms. The volume of spam can be so overwhelming that finding useful information within it becomes quite challenging. What exacerbates this issue is that spam can populate your public...
CISA Flags 8 Actively Exploited Flaws in Samsung and D-Link Devices
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed a set of eight flaws to the Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. This includes six shortcomings affecting Samsung smartphones and two...
Evasive Meduza Stealer Targets 19 Password Managers and 76 Crypto Wallets
In yet another sign of a lucrative crimeware-as-a-service (CaaS) ecosystem, cybersecurity researchers have discovered a new Windows-based information stealer called Meduza Stealer that's actively being developed by its author to evade detection by software solutions....
BlackCat Operators Distributing Ransomware Disguised as WinSCP via Malvertising
Threat actors associated with the BlackCat ransomware have been observed employing malvertising tricks to distribute rogue installers of the WinSCP file transfer application. "Malicious actors used malvertising to distribute a piece of malware via cloned webpages of...
IT Physical Security Policy
This policy will help your organization safeguard its hardware, software and data from exposure to persons (internal or external) who could intentionally or inadvertently harm your business and/or damage physical assets. From the policy: PHYSICAL SECURITY GUIDELINES...
