by Beck Bailey | Aug 5, 2023 | RSS
Threat actors are using an open-source rootkit called Reptile to target Linux systems in South Korea. “Unlike other rootkit malware that typically only provide concealment capabilities, Reptile goes a step further by offering a reverse shell, allowing threat...
by Beck Bailey | Aug 5, 2023 | RSS
Microsoft on Friday disclosed that it has addressed a critical security flaw impacting Power Platform, but not before it came under criticism for its failure to swiftly act on it. “The vulnerability could lead to unauthorized access to Custom Code functions used...
by Beck Bailey | Aug 5, 2023 | RSS
Cybersecurity researchers have discovered a new high-severity security flaw in PaperCut print management software for Windows that could result in remote code execution under specific circumstances. Tracked as CVE-2023-39143 (CVSS score: 8.4), the flaw impacts...
by Beck Bailey | Aug 4, 2023 | RSS
Discover the new shadow IT guidance published by the U.K.’s NCSC. Use this guide to better identify and reduce the levels of shadow IT within your organization.
by Beck Bailey | Aug 4, 2023 | RSS
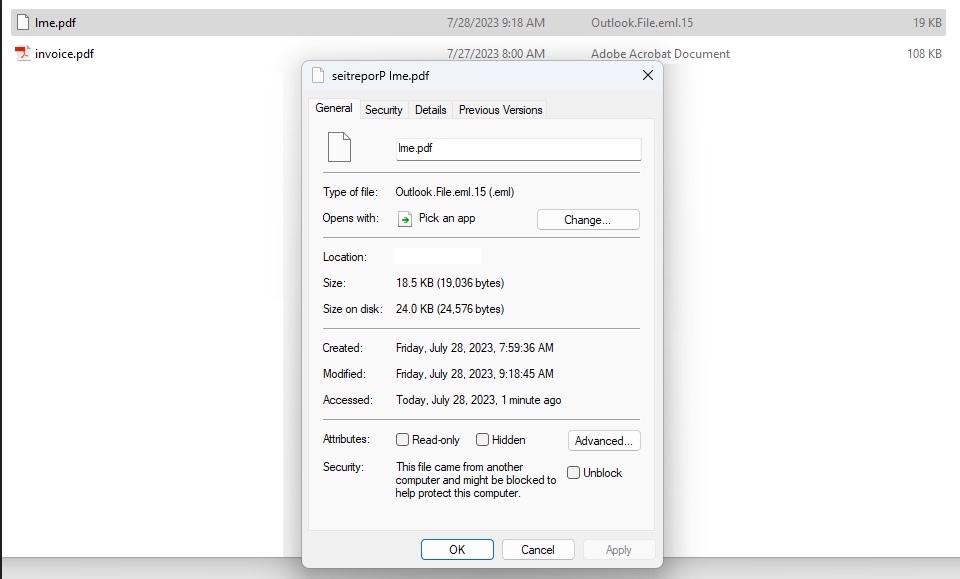
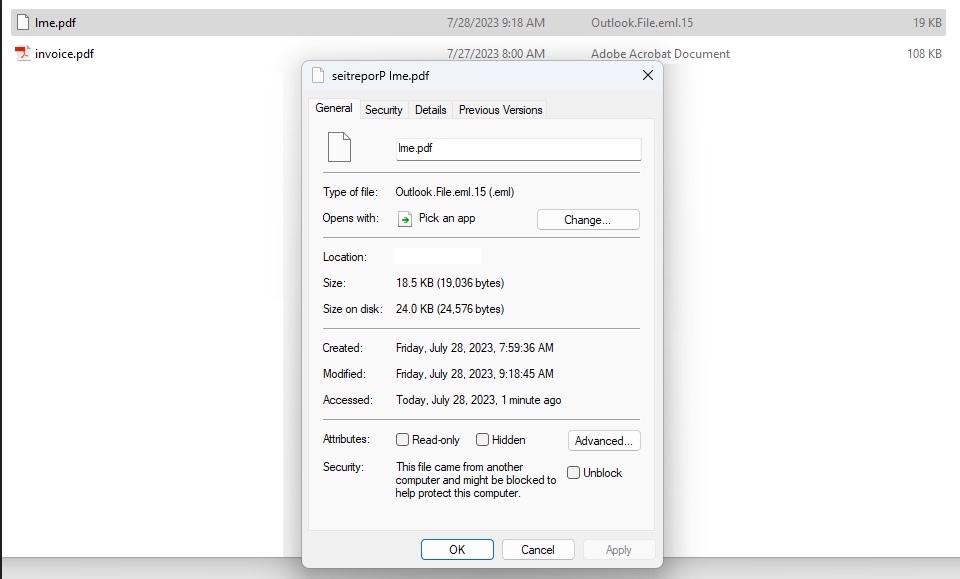
One frustrating aspect of email phishing is the frequency with which scammers fall back on tried-and-true methods that really have no business working these days. Like attaching a phishing email to a traditional, clean email message, or leveraging link redirects on...
Recent Comments