by Beck Bailey | Feb 1, 2024 | RSS
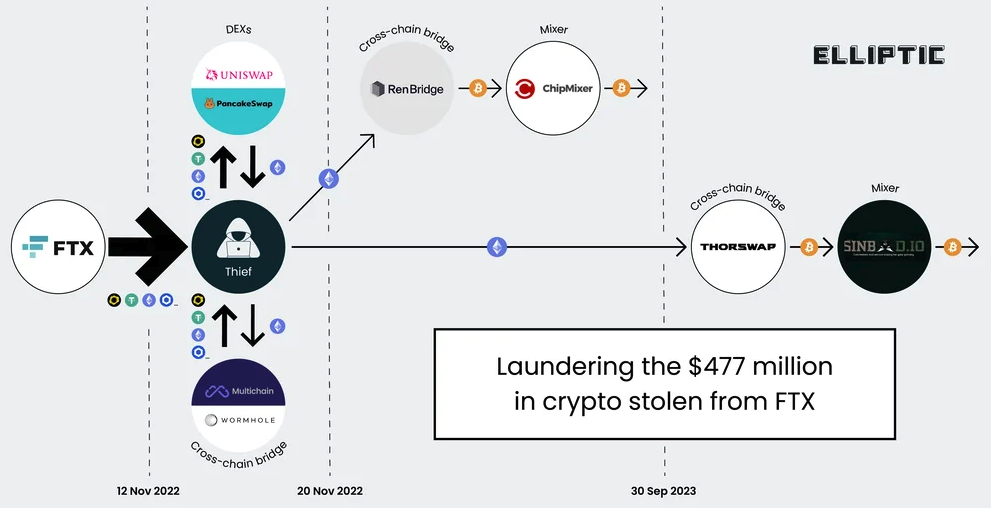
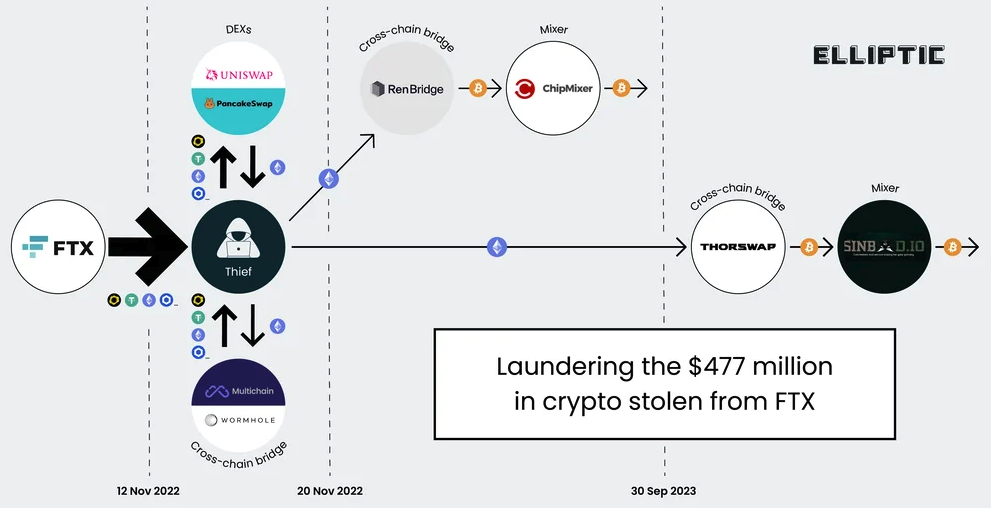
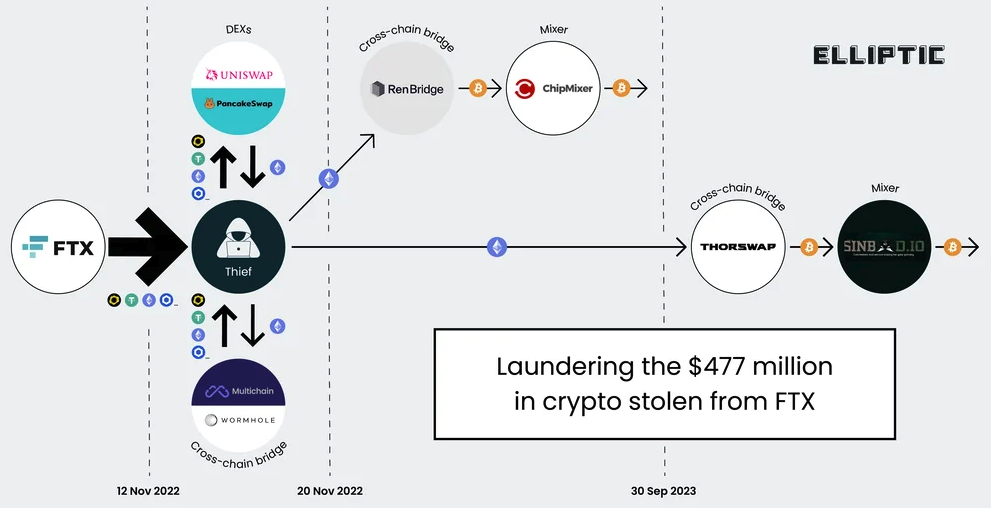
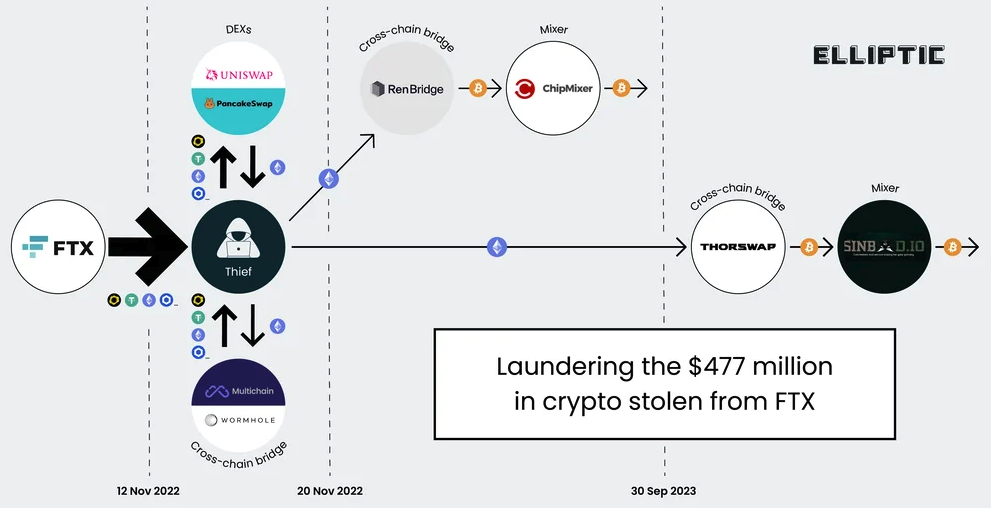
Three Americans were charged this week with stealing more than $400 million in a November 2022 SIM-swapping attack. The U.S. government did not name the victim organization, but there is every indication that the money was stolen from the now-defunct cryptocurrency...
by Beck Bailey | Feb 1, 2024 | RSS
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the Log4Shell vulnerability to propagate internally within an already compromised network. “The vulnerability is exploited in a brute-force...
by Beck Bailey | Feb 1, 2024 | RSS
Exposed Docker API endpoints over the internet are under assault from a sophisticated cryptojacking campaign called Commando Cat. “The campaign deploys a benign container generated using the Commando project,” Cado security researchers Nate Bill and Matt...
by Beck Bailey | Feb 1, 2024 | RSS
The U.S. government on Wednesday said it took steps to neutralize a botnet comprising hundreds of U.S.-based small office and home office (SOHO) routers hijacked by a China-linked state-sponsored threat actor called Volt Typhoon and blunt the impact posed by the...
by Beck Bailey | Feb 1, 2024 | RSS
How’s your vulnerability management program doing? Is it effective? A success? Let’s be honest, without the right metrics or analytics, how can you tell how well you’re doing, progressing, or if you’re getting ROI? If you’re not measuring, how do you know it’s...
Recent Comments